KeyStore Explorer – OSS Update
A month ago I wrote about a new owner having been identified for KeyStore Explorer (KSE). This post comprises an interim update on the new owner’s progress in taking over the application.
The new owner has been very busy over the last four weeks and has, in a relatively short space of time, removed all impediments to open sourcing the code base. This involved replacing a third party ASN.1 library (which was used extensively by KSE) with calls to Bouncy Castle.
In addition most of KSE’s icons were sourced from the commercial Icon Experience set. The new owner has replaced these icons with the Fugue set created by Yusuke Kamiyamane.
The new icons give the application a new look:
We have have also settled on an OSS license we are both comfortable with: GPL v3.
Upcoming work by the new owner will complete my unfinished work on new features for version 4.2 and perhaps add a few more items of functionality.
There is still a lot of work to be done but I am confident that KSE is in good hands.
Explore posts in the same categories: KeyStore Explorer, Open SourceTags: KeyStore Explorer
You can comment below, or link to this permanent URL from your own site.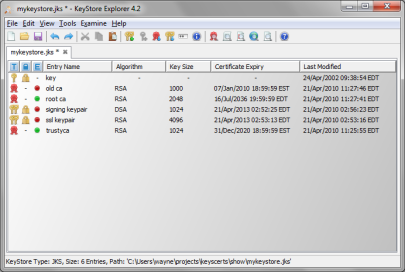
September 13, 2013 at 4:25 am
I have heard Java doesn’t have that great of a RNG. So how safe is using KSE for generating certs? If it is true that java doesn’t have good random numbers doesn’t that make it inadequate for certificate generation?
September 13, 2013 at 4:48 am
You’ll need to give me a little more to go on than that if you want my opinion on it. Do you have a reference to any details?
September 13, 2013 at 1:24 pm
After looking into it more it seems like java.util.Random is the bad RNG, but they actually have a SecureRandom that is suppose to be cryptographically secure. I assume you use the SecureRandom.
September 13, 2013 at 1:57 pm
That’s right Phillip, KSE uses SecureRandom.
February 17, 2014 at 10:29 pm
First of all: Congrats on the new Owner and the progress, thats big news.
Regarding the State of Randomness in Java there are some problems with SecureRandom in Oracle or OpenJDK Java. They are not so critical for every day usage, but generating keys (especially with 256bit) is another thing. A good writeup (before some fixes have been implemented) can be found here:
There are some PRNG implementations which have a larger state and also are better useable with untrusted entropy sources. Fortuna is one – there was a discussion to inlcude it in BC, but I am not sure what its current state is. There are GPL stand alone versions available.
February 17, 2014 at 10:44 pm
Interesting paper, thanks for posting it. I’ll leave it to the new owner and the OSS community to address it as solutions emerge though. I’m done with KSE.